What is a Cybersecurity Incident Response Plan (CSIRP)?
A Cyber Security Incident Response Plan (CSIRP) is a documented framework that defines how an organization identifies, responds to, manages, and recovers from cybersecurity incidents, including data breaches, ransomware attacks, phishing, and unauthorized system access.
An effective incident response plan helps organizations minimize damage, reduce downtime, meet regulatory requirements, and demonstrate due diligence during audits or investigations.
Why is a CSIRP needed?
- Standardizes documentation so incident records are consistent and defensible
- Clarifies decision rights to reduce delays during high-pressure incidents
- Supports breach determination and notification planning with Legal/Privacy workflows
- Improves audit readiness by making artifacts easy to produce and review
- Creates a continuous improvement loop (lessons learned → tracked corrective actions)
Compliance & Regulatory Frameworks Covered
This incident response plan template suite is designed to support compliance with widely recognized frameworks and regulations, including:
- HIPAA Security Rule
- NIST Cybersecurity Framework
- PCI DSS
- ISO/IEC 27001
- FTC Safeguards Rule
- State Data Breach Notification Laws
- EU frameworks that emphasize incident handling and reporting.
Regulatory requirements vary by jurisdiction and industry. Many frameworks explicitly require incident response plans/procedures or create notification and documentation obligations that necessitate a formal plan. The templates help organizations document required processes for detection, response, mitigation, and reporting of security incidents.
Benefits of a compliance-grade CSIRP
- Demonstrates governance with clear ownership, authority, and escalation paths
- Supports timely and consistent notifications when required
- Improves evidence handling and defensibility (decision trail, meeting notes, action tracking)
- Reduces audit friction with standardized artifacts and repeatable processes
Cyber Security Incident Response Plan Template Suite (Compliance‑Ready)
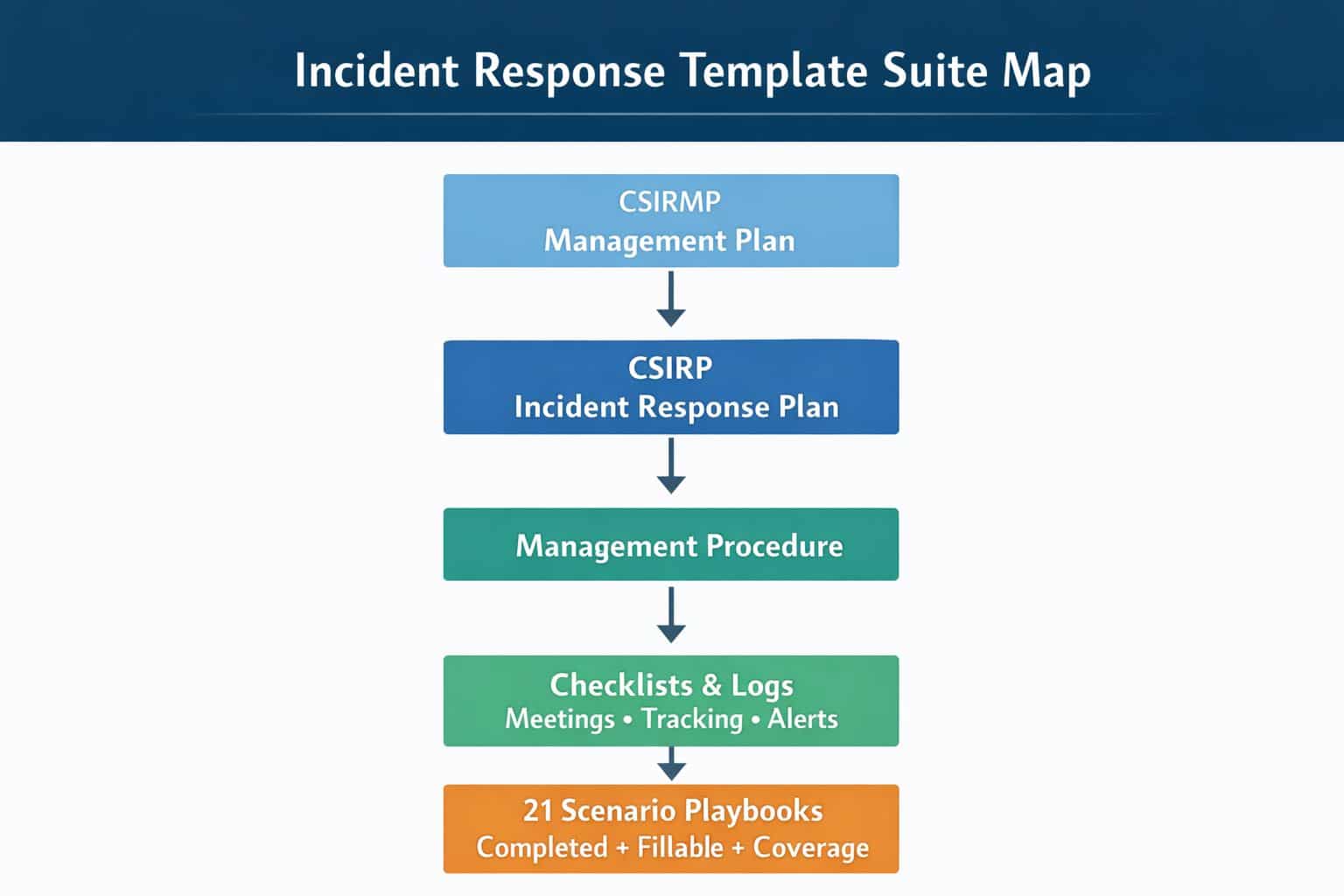
Regulators, auditors, customers, and cyber insurers increasingly expect incident response to be governed, documented, and repeatable. This suite provides 13 core templates and 21 scenario playbooks (completed examples + client-fill templates) so your organization can implement a defensible enterprise incident response program quickly.
How the template suite helps
The CSIRMP establishes governance; the CSIRP and Management Procedure operationalize response; checklists and logs reduce missed steps; and scenario playbooks provide completed examples that show what high-quality documentation looks like.
What’s Included: 13 Core Templates
Step-by-step Guide for How to Use the Templates
A structured onboarding path that explains how the suite fits together and what to customize first. It accelerates adoption and reduces the risk of partial implementation.
Cyber Security Incident Response Management Plan (CSIRMP)
The governance backbone: authority, escalation, communications approvals, training/testing, and continuous improvement. Helps ensure incident response runs as a business process, not an improvised technical event.
Cyber Security Incident Response Plan (CSIRP)
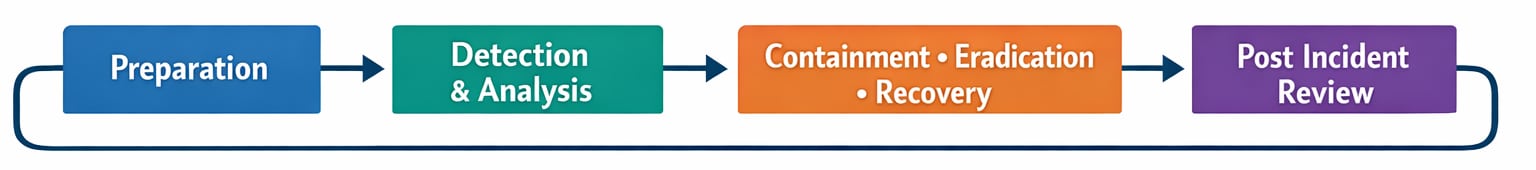
The operational plan teams use during incidents across detection, containment, eradication, recovery, and closeout. Provides consistent phase outputs and documentation expectations.
Cyber Security Incident Response Management Procedure
Defines how to run the incident: cadence, roles, war room mechanics, documentation rhythm, and handoffs. Turns the plan into repeatable execution.
Cyber Security Incident Response Plan Checklist
A phase-based checklist to reduce missed steps under pressure and keep response defensible. Useful for facilitators and incident commanders to confirm completion gates.
Cyber Security Incident Response Preparation Checklist
Validates readiness: people, tools, access, comms, playbooks, exercises, and evidence handling readiness. Helps identify gaps before a real incident.
Cyber Security Vulnerability Response Checklist
Standardizes vulnerability intake, triage, remediation, verification, and escalation when exploitation is suspected. Connects vulnerability management to incident response maturity.
CSIRT Meeting Agenda
A structured agenda that keeps meetings outcome-driven: status, risks, decisions, actions, and next steps. Prevents war rooms from devolving into unstructured updates.
CSIRT Meeting Notes
Captures decisions, approvals, facts/unknowns, and action items in a consistent format. Supports auditability, handoffs, and post-incident reporting.
Initial Internal Management Security Incident Alert
A first-hour executive alert template focused on impact, scope, decisions required, and next update cadence. Improves leadership alignment and reduces rumor-driven escalation.
CSIRT Issues and Goals List
Tracks the core problems to solve and the response objectives (what “done” looks like). Helps manage scope creep and keeps teams aligned on outcomes.
CSIRT Action Tracking List
The single source of truth for tasks, owners, due dates, dependencies, and status. Improves accountability and follow-through during fast-moving incidents.
CSIRT Member Activity Tracking Log
A time-stamped record of key responder actions and outcomes. Supports timeline reconstruction, defensibility, and after-action reviews.
Scenario Templates (21) — Completed Example + Client Fillable
Each scenario includes: (1) a Completed Example, (2) a Client Fillable Template, and (3) a 1‑page Coverage Checklist Appendix.
Compromised Database Server
Guides containment, credential rotation, integrity validation, and safe restoration of high-value data systems. Includes documentation for access paths, impact, and recovery approvals.
Worm Distributed Denial of Service (DDoS) Agent Infestation
Focuses on rapid isolation, segmentation, eradication verification, and minimizing collateral network impact. Helps coordinate large-scale endpoint response across teams.
Stolen Documents
Supports investigations for unauthorized access to sensitive files, scoping exposure, and controlling access. Emphasizes Legal/Comms coordination and defensible documentation.
Domain Name System (DNS) Server Denial of Service (DoS)
Covers provider coordination, failover decisions, service status communications, and recovery validation. Useful for business continuity and stakeholder updates during outages.
Unknown Exfiltration
Designed for ambiguity: suspected data loss without full scope certainty. Emphasizes evidence preservation, scoping methodology, and controlled containment.
Unauthorized Access to Payroll Records
Integrates HR, Legal, and privacy considerations for workforce data incidents. Guides breach determination support and internal communications discipline.
Disappearing Host
Addresses wiped/missing hosts and potential attacker cleanup. Includes asset inventory validation, logging gaps, rebuild decisions, and broader compromise assessment.
Telecommuting Compromise
Covers remote endpoint compromise and credential response, including safe re-onboarding of the user/device. Includes practical guidance for remote-work realities.
Anonymous Threat
Provides a credibility assessment workflow and escalation logic for extortion emails or anonymous warnings. Helps document rationale and avoid overreaction while staying prepared.
Peer-to-Peer File Sharing
Guides response to policy violations and data leakage risk from P2P tools. Includes verification, HR/legal coordination, and closure documentation.
Unknown Wireless Access Point
Covers discovery, physical validation, containment, and scope assessment of rogue AP activity. Provides steps to validate connected devices and prevent recurrence.
Ransomware with Data Theft (Double Extortion)
Structures containment, restoration gating, and decision-making under leak-site pressure. Includes executive decision points and communications control patterns.
Business Email Compromise (BEC) / Fraudulent Payment
Focuses on rapid mailbox investigation, banking coordination, persistence checks, and fraud containment. Includes documentation for approvals and timeline capture.
Cloud Storage Misconfiguration (Public Bucket/Container Exposure)
Guides rapid lockdown, access-log scoping, exposure window determination, and shared responsibility clarity. Includes guardrails to prevent recurrence (policies/controls).
Third-Party / Vendor Compromise (SaaS Provider / MSP Compromise)
Provides steps for contractual notifications, evidence requests, and internal impact assessment. Supports stakeholder communications and downstream risk decisions.
Insider Data Theft
Balances HR and Legal boundaries with evidence handling and privilege management. Provides a defensible structure for access review, containment, and investigation.
Credential Stuffing / Account Takeover
Covers detection signals, rate limiting, forced resets, session invalidation, and support coordination. Includes customer-impact documentation and stabilization steps.
Web Application Vulnerability Exploitation
Guides investigation and patch decisions under uncertainty, including compensating controls (e.g., WAF). Includes recovery validation and monitoring gates.
Compromised Privileged Identity / IAM Misconfiguration (Cloud Role Abuse)
Focuses on session/key rotation, access restriction, cloud log preservation, and blast-radius assessment. Includes controlled restoration of privileged paths and approvals.
Cryptomining / Resource Hijacking (Cloud Spend Spike)
Covers detection, containment of malicious workloads, cost controls, and guardrails/hardening. Includes FinOps/ops coordination and validation steps.
Lost/Stolen Endpoint with Sensitive Data (Laptop/Mobile)
Guides encryption verification, remote wipe/lockout, credential resets, and exposure determination. Includes notification decision support and secure replacement onboarding.
Contact us if you have any questions or need to see any samples.
Cyber Security Incident Response Plan – Frequently Asked Questions
What is a cyber security incident response plan?
A cyber security incident response plan is a documented set of procedures that guides how an organization detects, responds to, contains, and recovers from cybersecurity incidents.
Why is an incident response plan required for compliance?
Regulations such as HIPAA, PCI DSS, and NIST require organizations to maintain documented incident response procedures to ensure timely detection, mitigation, and reporting of security incidents.
What is included in an incident response template suite?
An incident response template suite typically includes policies, response playbooks, communication plans, incident logs, breach notification checklists, and post-incident review documentation.
Is this incident response plan suitable for HIPAA compliance?
Yes. The templates are designed to align with HIPAA Security Rule requirements and help covered entities and business associates document compliant incident response processes.
How often should an incident response plan be updated?
Incident response plans should be reviewed at least annually and updated after significant security incidents, regulatory changes, or organizational changes.
What is the difference between an incident response plan and a playbook?
An incident response plan outlines the overall framework and responsibilities, while playbooks provide step-by-step instructions for responding to specific types of incidents such as ransomware or phishing attacks.





